Can You Use Terminal Services In A Workgroup
The RD Gateway is designed to secure access to remote desktop deployments from untrusted networks. At that place are several options for its placement in the network. Another benchmark is whether and how to integrate it with Advertisement.
- Author
- Contempo Posts
![]()
The RD Gateway allows RDP clients to communicate over the internet through an HTTPS tunnel, thus saving organizations the need to prepare up a VPN. Talking to the RD Session Host, the gateway uses pure RDP on port 3389 by default. Access can be restricted to certain resources and users.
Relationship to RD Web Access ^
The RD Gateway is 1 of several server roles for Remote Desktop Services. RD Web Access, another RDS role, is besides an entry bespeak for remote desktop clients. Information technology allows the kickoff of a desktop or a RemoteApp from the web browser.

Remote Desktop in RD Web Access
Accordingly, 1 could assume that RD Web Admission could exist used equally an alternative to an RD Gateway. Only this is not the case. As expected, the clients tin can likewise admission the spider web interface via HTTPS, merely opening an application leads to an unsecured RDP connection to a session host. RD Web Access tin can, all the same, be combined with a gateway to make admission easier for users.
Placement of the gateway in the internal network ^
In a simple configuration, you could identify the RD Gateway in the LAN and open firewall port 443 for external access to the gateway. You also need a public DNS tape so that clients can resolve the name of the gateway.

How a reverse proxy works
Notwithstanding, this configuration is non very secure, as information technology allows an intruder to movement laterally through the network if he compromises the RD Gateway. You lot can therefore protect it past placing a opposite proxy in the DMZ, which frontward the requests via HTTPS through the firewall to the gateway.
Gateway in the DMZ ^
Alternative deployment options assume that an RD Gateway does not run in the internal network, simply rather in the DMZ, which is usually shielded internally and externally by firewalls.
In the internal facing firewall, port 3389 must exist open up for the RDP toward the LAN and externally port 443 for the SSL connection from the net. However, if the RD Gateway is a member of an Ad domain, so a whole series of ports must be opened toward the internal network for communication with the DC.
An older post from Microsoft's RDS Team Blog lists the following functions that require access to internal resources:
- Authentication and authorization of users
- Resolving the names of internal resources
- Obtaining the certificate revocation list
- Sending RADIUS requests (if a central NPS server is used)

Communication of an RD Gateway in the DMZ, which is a member of a domain, with the internal network
Reduced traffic with a workgroup server ^
Much of this communication tin can be avoided past configuring the RD Gateway as a workgroup server instead of joining it to an AD domain. This has been supported since Windows Server 2008 R2.
But the configuration is more than circuitous than with a fellow member server, then you have to manage all permitted users locally. In addition, GPOs are no longer available for the direction of the server, and local group policies must exist used instead.
RODC in the DMZ ^
To avert extensive communication with a domain controller in the LAN and still not take to forgo the AD integration, it makes sense to place a read-only domain controller (RODC) in the DMZ.

An RODC in the DMZ authenticates remote desktop users and reduces traffic to the internal network
The RODC belongs to the internal AD forest and authenticates remote desktop users. Its advice with the internal network is restricted to replication with the DCs in the LAN.
Dedicated woods in the DMZ ^
A like result can exist achieved if you set upwardly your ain wood in the DMZ and create a unidirectional trust relationship to the internal forest. The RDS Gateway is a member of the DMZ domain; hence, the RDP users authenticate against the DC there.
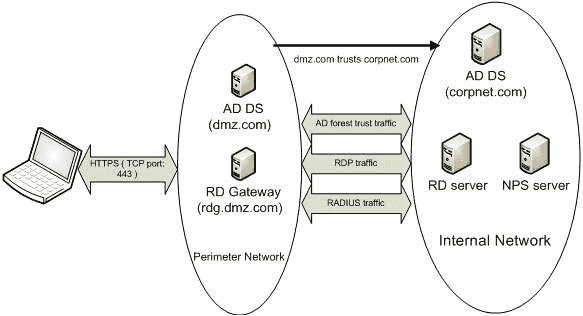
A topology with its own Advert forest in the DMZ, which is connected to the internal wood via a one way trust
Hither, Advertisement-related traffic is reduced to that which is necessary for the trust relationship.
Subscribe to 4sysops newsletter!
Likewise read: Install RD Gateway, assign a certificate, and configure CAP and RAP
Can You Use Terminal Services In A Workgroup,
Source: https://4sysops.com/archives/rd-gateway-deployment-options-workgroup-or-domain-joined/
Posted by: frazierbincepuld.blogspot.com


0 Response to "Can You Use Terminal Services In A Workgroup"
Post a Comment